VMware 2v0-21-23 practice test
VMware vSphere 8.x Professional
Last exam update: Jul 20 ,2024
Question 1
An administrator needs to provide encryption for workloads within an existing vSphere cluster.
The following requirements must be met:
Workloads should be encrypted at rest.
Encrypted workloads must automatically be encrypted during transit.
Encryption should not require any specific hardware.
What should the administrator configure to meet these requirements?
- A. Encrypted vSphere vMotion
- B. Unified Extensible Firmware Interface (UEFI) Secure Boot
- C. Host Encryption
- D. VM Encryption
Answer:
c
Question 2
An administrator creates a virtual machine that contains the latest company-approved software, tools and security updates. Company policy requires that only full clones are allowed for server workloads.
A combination of which two tasks should the administrator complete to prepare for the deployment of this virtual machine for multiple users? (Choose two.)
- A. Set appropriate permissions on the virtual machine.
- B. Create a virtual machine customization specification.
- C. Upgrade the virtual hardware.
- D. Convert the virtual machine to a template.
- E. Take a snapshot of the virtual machine.
Answer:
ab
Question 3
An administrator wants to allow a DevOps engineer the ability to delete Tanzu Kubernetes Grid (TKG) cluster objects in a vSphere Namespace.
Which role would provide the minimum required permissions to perform this operation?
- A. Administrator
- B. Can View
- C. Owner
- D. Can Edit
Answer:
d
Question 4
If a distributed switch uses the Route based on physical NIC load load balancing algorithm, what does the mean send or receive utilization of an uplink need to exceed for the flow of traffic to move to the second uplink?
- A. 75 percent of the capacity over a 30 second period
- B. 60 percent of the capacity over a 30 second period
- C. 60 percent of the capacity over a 40 second period
- D. 75 percent of the capacity over a 40 second period
Answer:
b
Question 5
Refer to the exhibit.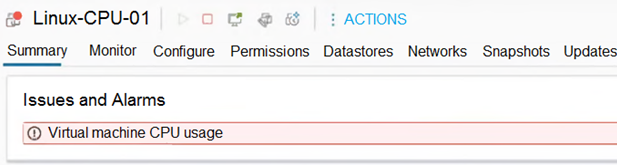
After removing an ESXi host from a cluster for maintenance, a number of virtual machines have encountered the warning seen in the exhibit.
After re-adding the ESXi, the issue is resolved.
Which step should the administrator take to move the triggered alarm to its normal state?
- A. Ignore
- B. Acknowledge
- C. Disable
- D. Reset to Green
Answer:
d
Question 6
An administrator has a host profile named Standard-Config. The administrator wants to change the other host profiles to use only the storage configuration settings that are defined in the Standard-Config host profile.
What should the administrator do to make this change?
- A. Export host customizations and import them to the other host profiles.
- B. Copy the storage settings from Standard-Config to all other host profiles.
- C. Duplicate the Standard-Config host profile and only modify the storage configuration settings.
- D. Export the Standard-Config host profile and attach it to tile other hosts.
Answer:
b
Question 7
An administrator has a requirement to revert a running virtual machine to a previous snapshot af-ter a failed attempt to upgrade an application. When the administrator originally took the snap-shot, the following choices in the Take Snapshot dialog were made:
Snapshot the virtual machines memory = false
Quiesce guest file system = false
What will be the result of the administrator selecting the Revert to Latest Snapshot option to return the virtual machine to a previous snapshot? (Choose two.)
- A. The virtual machine will be restored to the parent snapshot
- B. The virtual machine will be restored in a powered off state.
- C. The virtual machine will be restored to the child snapshot
- D. The virtual machine will be restored in a powered on state.
- E. The virtual machine will be restored in a suspended state.
Answer:
ad
Question 8
An administrator needs to create affinity rules for the following vSphere cluster setup:
The cluster contains two virtual machines (VMs) named app01 and app02.
The cluster contains six hosts named esx11 through esx16.
The app01 and app02 VMs run software that is licensed to run only on esx11, esx12, or esx13.
vSphere Distributed Resource Scheduler (DRS) is configured.
Which set of steps must the administrator perform to ensure that the licensing requirements are met for app01 and app02?
- A. 1. Add all the hosts to a host group.2. Create a VM-VM anti-affinity rule for app01 and app02.
- B. 1. Add the esx11 esx13 hosts to a host group.2. Create a VM-VM affinity rule for app01 and app02.
- C. 1. Add the VMs to a VM group and the esx11 esx13 hosts to a host group.2. Create a VM-Host required rule between the VM group and the host group.
- D. 1. Add the VMs to a VM group and the esx11 esx13 hosts to a host group.2. Create a VM-Host preferential rule between the VM group and the host group.
Answer:
c
Question 9
An administrator is tasked with allowing a single user the ability to take snapshots on a virtual machine. When looking in vCenter, the administrator can see that there are already users and groups assigned permissions on the virtual machine as follows:
The group VM_Users has the Virtual Machine Power User role.
The group VM_Viewers has the Read Only role.
The administrator confirms that the user requesting the additional access is currently one of five members of the VM_Viewers group.
Which two steps should the administrator take to grant this user the additional access required without impacting the user access of others? (Choose two.)
- A. Add the user to the VM_Users group and leave the permissions on the virtual machine object unchanged.
- B. Add a new permission on the virtual machine object selecting the user and the new custom role.
- C. Edit the Read Only role to add the Virtual Machine Snapshot Management privileges.
- D. Create a new custom role with the Virtual Machine Snapshot Management privileges.
- E. Add a new permission on the virtual machine object selecting the VM_Viewers group and the new custom role.
Answer:
bd
Question 10
An administrator is tasked with migrating a single virtual machine (VM) from an existing VMware vCenter to a secure environment where corporate security policy requires that all VMs be encrypted. The secure environment consists of a dedicated vCenter instance with a 4-node vSphere cluster and already contains a number of encrypted VMs.
Which two steps must the administrator take to ensure the migration is a success? (Choose two.)
- A. Ensure that the source and destination vCenter instances share the same Key Management Server (KMS).
- B. Ensure that Encrypted vMotion is turned off for the VM.
- C. Ensure that the VM is encrypted before attempting the migration.
- D. Ensure that the VM is powered off before attempting the migration.
- E. Ensure that the source and destination vCenter Servers have a different Key Management Server (KMS).
Answer:
ac