oracle 1z0-588 practice test
Oracle Hyperion Data Relationship Management Essentials Exam
Last exam update: Jul 20 ,2024
Question 1
You decide to implement node type? for the Account dimension. What are the required steps that
must be completed to implement a node type?
1. Under Administer, create node types with valid assigned DRM elements.
2. Create a hierarchy property that contains a list of values that matches the node types defined.
3. Create a local node property called "HierarchyNodeType".
4. For version, set the HierarchyNodeType to "Dimension".
5. For the hierarchy, set the Dimension property to the desired Node type value (for example.
Account dimension type for the Account hierarchy).
6. Upload a glyph for each node type.
- A. 1, 2, 3, 5 only
- B. 1, 3, 4, 5 only
- C. 1, 2, 3, 4, 5 only
- D. 1, 2, 3, 5, 6 only
- E. 1, 2, 3, 4, 5, 6
Answer:
B
Question 2
You maintain the Market hierarchy in DRM.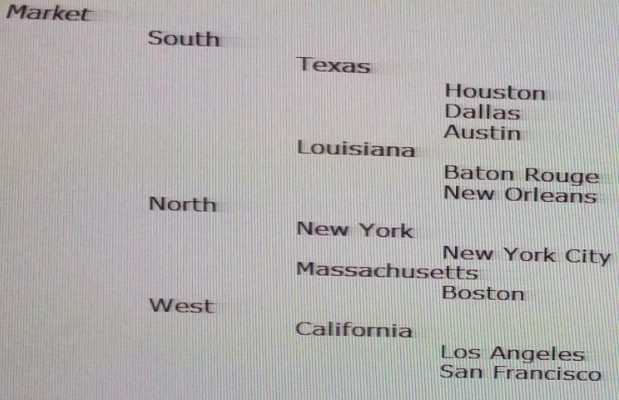
A target system needs an alternate hierarchy of the Market dimension that contains the lowest level
of markets (city) rolling up by market size (nodes Large, Medium, and Small).
Identify the ways to meet this requirement in DRM.
1. Create a property category called "Market Size" and populate the values as "Large", "Medium",
and "Small"
2. Create a property called "Market Size" and populate the values as "Large", "Medium", and "Small"
3. Create a node type called "Market Size" and populate the values as "Large", "Medium", and
"Small"
4. Create an alternate hierarchy in the Market dimension with nodes "Large", "Medium", and
"Small". Add cities as shared nodes under the appropriate Market Size nodes.
- A. 1 only
- B. 2 only
- C. 3 only
- D. 4 only
- E. 1, 4 only
- F. 2, 4 only
- G. 2, 3, 4 only
Answer:
D
Question 3
The Data Relationship Management API Adapter is required for the DRM API. Identify three other
components that are required to use the DRM API.
- A. Oracle WebLogic Server 11g
- B. JDeveloper
- C. EPM Workspace
- D. Oracle Web Services Manager (OWSM)
- E. Shared Services
Answer:
CDE
Question 4
Per the Example: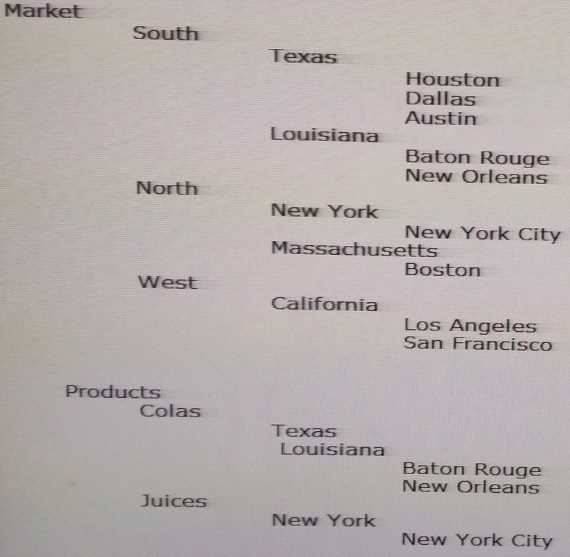
You need to load both the Product and Market hierarchies to multiple Essbase databases.
Identify three DRM objects that could be used across both Product and Market hierarchies?
- A. Common Essbase system properties
- B. Common Essbase system validations
- C. Parent/Child export definitions
- D. Generation export definitions
- E. Level export definitions
Answer:
ABC
Question 5
Per the example: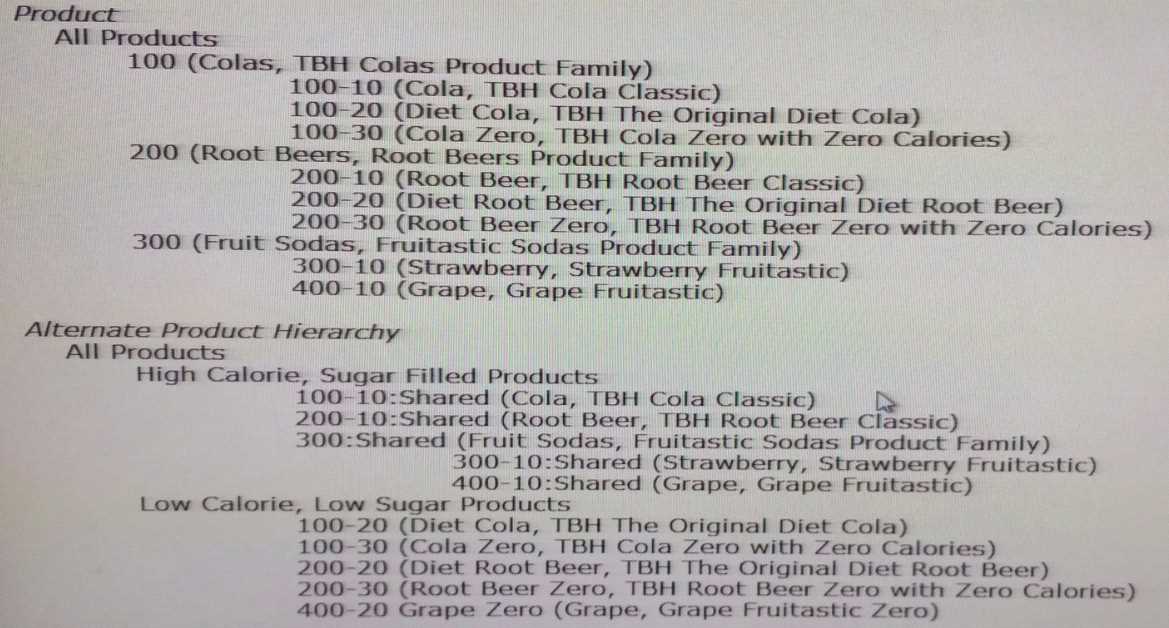
Identify the two true Statements about the Product hierarchy and its alternate hierarchy.
- A. 300-10 is called an Explicit Shared Node.
- B. 300-10 is called an Implicit Shared Node.
- C. 300 is not a valid shared node because only leaf nodes may be shared.
- D. You can delete the node 300-10 in the alternate product hierarchy,
- E. You can change local property values in the alternate product hierarchy.
- F. You can change any of the system generated property values on the Shared Node property category for the alternate product hierarchy.
Answer:
EF
Question 6
Identify the three benefits of adding a standard prefix to a related set of property definitions.
- A. Provides faster performance
- B. Easier to find a group of related properties when creating an Export
- C. Prevents conflicts when a property definition in two target or source dimensions have the same name
- D. The prefix can be used as criteria when creating a filter for a Query
- E. DRM sorts property definitions alphabetically by default
Answer:
ABC
Question 7
Identify the two true statements about node access groups.
- A. Node access groups use inheritance to assign the same access to descendants of a node but this inherited security may be overwritten at lower levels.
- B. Valid node access levels are Read, Edit, LimitedEdit, Insert, Inactivate, and Add.
- C. Access levels are assigned separately for leaf and limb nodes.
- D. Node access groups can be used to filter the display of the hierarchy so that users only see the section of the hierarchy for which they have access.
- E. Node access groups may be assigned by the Application Administrator or Access Manager.
Answer:
BE
Question 8
Identify the two true statements about user permissions.
- A. Administrators assign a permission level to a user; and based on that permission, a role is associated to that user.
- B. If a user has conflicting levels of access, the lowest level of access is assigned.
- C. You can set up a security administrator who only has access to user management and no access to create or manage data and metadata within DRM.
- D. DRM uses Property Categories to assign security access for Property Definitions.
- E. Security in DRM can be assigned by Version, Hierarchy, Property Category, and Property Definition.
Answer:
CD
Question 9
A user has been assigned the Data Creator role. Identify the two true statements.
- A. The user can access a query created by a user with the Interactive User role.
- B. The user can access a query created by themselves.
- C. The user can access all standard queries.
- D. The user can access all system queries.
- E. The user can create standard queries.
Answer:
DE
Question 10
What are valid workflow operations in DRM?
1. Create requests
2. Approve requests
3. Save requests
4. Merge requests
5. Cancel requests
- A. 1, 2, 4 only
- B. 1, 2, 3, 4 only
- C. 1, 2, 3 only
- D. 1, 2, 4, 5 only
- E. 3, 4, 5 only
Answer:
E
Question 11
Which API method is used to check the status of an asynchronous operation executed via the DRM
web service?
- A. getJobStatus
- B. checkJobStatus
- C. getJobInfo
- D. checkStatus
- E. getOperationstates
Answer:
B
Question 12
Per the example: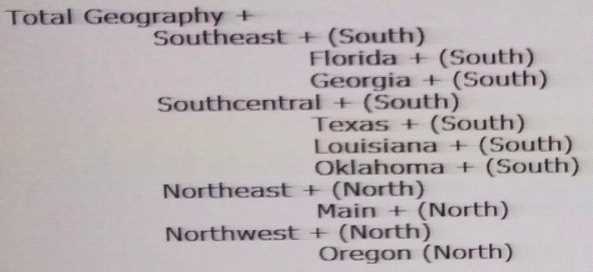
You have a property definition called Region with possible valid values "east", "West", "North", and
"South".
How do you set this property for end users?
- A. Because most of the states are in the South, set the default value to South.
- B. Turn on inheritance for the property.
- C. Set up the property to derive the "South" value.
- D. Set the property to Global.
- E. Create a lookup property so that users can easily select "South" from a drop down menu.
Answer:
A
Question 13
Identify the three true statements about the timing of DRM integrations.
- A. Exports may be run any time on any version.
- B. Imports may be run any time on any version.
- C. Property queries may be run any time on any version.
- D. DRM integrations may be scheduled or run on demand.
- E. Once a version has been finalized, only data Managers may run exports.
Answer:
CDE
Question 14
You have three hierarchies for the Entity dimension. One hierarchy rolls up entities by geography,
one hierarchy rolls up entities by function, and one hierarchy rolls up entities by legal structure. In
your Hyperion Financial Management (HFM) application, these three hierarchies exist within a single
Entity dimension. You want to be able to manage the properties for the nodes once.
Identify the three ways that DRM can be designed to support this requirement.
- A. Maintain the three separate DRM hierarchies within a single version with the HFM properties set to Global; combine the hierarchies into a single export.
- B. Create the three structures in a single DRM hierarchy with the Geography hierarchy as the primary hierarchy and the Function and Legal structures as shared nodes.
- C. Maintain each hierarchy in its own version; set the Geography hierarchy to Primary and the Function and Legal hierarchies to Shared.
- D. Maintain the three separate DRM hierarchies within a single version with the HFM properties set to Global and combine the hierarchies into a single export book.
- E. Maintain the three separate DRM hierarchies within a single version with the HFM properties set to Global; Use the Blend feature to combine the hierarchies into a single export.
Answer:
ABC
Question 15
Identify the four true statements about designing property categories, property definitions, and
validations for target and source systems.
- A. Allow users to type in property values for properties that only have a limited set of valid values.
- B. Create derived property definitions that are hidden from users that can be used in exports for target systems.
- C. Create separate property categories for each target and source system.
- D. Name property definitions different then target system names.
- E. Create similar validations that are used by source systems.
- F. Create similar validations that are used by target systems.
Answer:
BCDE