microsoft sc-200 practice test
Microsoft Security Operations Analyst
Note: Test Case questions are at the end of the exam
Last exam update: Jul 20 ,2024
Question 1 Topic 6, Mixed Questions
HOTSPOT
You deploy Azure Sentinel.
You need to implement connectors in Azure Sentinel to monitor Microsoft Teams and Linux virtual machines in Azure. The
solution must minimize administrative effort.
Which data connector type should you use for each workload? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area: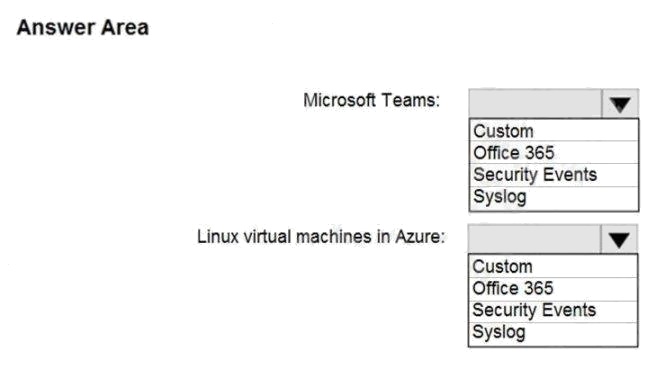
Answer:
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-office-365 https://docs.microsoft.com/en-us/azure/sentinel/connect-
syslog
Question 2 Topic 6, Mixed Questions
You use Azure Sentinel.
You need to receive an alert in near real-time whenever Azure Storage account keys are enumerated.
Which two actions should you perform? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. Create a livestream
- B. Add a data connector
- C. Create an analytics rule
- D. Create a hunting query.
- E. Create a bookmark.
Answer:
B D
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/livestream
Question 3 Topic 6, Mixed Questions
You plan to create a custom Azure Sentinel query that will provide a visual representation of the security alerts generated by
Azure Security Center.
You need to create a query that will be used to display a bar graph.
What should you include in the query?
- A. extend
- B. bin
- C. count
- D. workspace
Answer:
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/azure-monitor/visualize/workbooks-chart-visualizations
Question 4 Topic 6, Mixed Questions
You need to visualize Azure Sentinel data and enrich the data by using third-party data sources to identify indicators of
compromise (IoC).
What should you use?
- A. notebooks in Azure Sentinel
- B. Microsoft Cloud App Security
- C. Azure Monitor
- D. hunting queries in Azure Sentinel
Answer:
A
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/notebooks
Question 5 Topic 6, Mixed Questions
You are configuring Azure Sentinel.
You need to send a Microsoft Teams message to a channel whenever a sign-in from a suspicious IP address is detected.
Which two actions should you perform in Azure Sentinel? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. Add a playbook.
- B. Associate a playbook to an incident.
- C. Enable Entity behavior analytics.
- D. Create a workbook.
- E. Enable the Fusion rule.
Answer:
A B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
Question 6 Topic 6, Mixed Questions
You plan to create a custom Azure Sentinel query that will track anomalous Azure Active Directory (Azure AD) sign-in activity
and present the activity as a time chart aggregated by day.
You need to create a query that will be used to display the time chart.
What should you include in the query?
- A. extend
- B. bin
- C. makeset
- D. workspace
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/azure-monitor/logs/get-started-queries
Question 7 Topic 6, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is
detected.
Solution: You create a Microsoft incident creation rule for a data connector.
Does this meet the goal?
- A. Yes
- B. No
Answer:
A
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-security-center
Question 8 Topic 6, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is
detected.
Solution: You create a hunting bookmark.
Does this meet the goal?
- A. Yes
- B. No
Answer:
B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-security-center
Question 9 Topic 6, Mixed Questions
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains a
unique solution that might meet the stated goals. Some question sets might have more than one correct solution, while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not appear in
the review screen.
You are configuring Azure Sentinel.
You need to create an incident in Azure Sentinel when a sign-in to an Azure virtual machine from a malicious IP address is
detected.
Solution: You create a scheduled query rule for a data connector.
Does this meet the goal?
- A. Yes
- B. No
Answer:
B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-azure-security-center
Question 10 Topic 6, Mixed Questions
You create a custom analytics rule to detect threats in Azure Sentinel.
You discover that the rule fails intermittently.
What are two possible causes of the failures? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
- A. The rule query takes too long to run and times out.
- B. The target workspace was deleted.
- C. Permissions to the data sources of the rule query were modified.
- D. There are connectivity issues between the data sources and Log Analytics
Answer:
A D
Explanation:
Incorrect Answers:
B: This would cause it to fail every time, not just intermittently.
C: This would cause it to fail every time, not just intermittently.
Question 11 Topic 6, Mixed Questions
You have an Azure Sentinel deployment in the East US Azure region.
You create a Log Analytics workspace named LogsWest in the West US Azure region.
You need to ensure that you can use scheduled analytics rules in the existing Azure Sentinel deployment to generate alerts
based on queries to LogsWest.
What should you do first?
- A. Deploy Azure Data Catalog to the West US Azure region.
- B. Modify the workspace settings of the existing Azure Sentinel deployment.
- C. Add Azure Sentinel to a workspace.
- D. Create a data connector in Azure Sentinel.
Answer:
C
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/extend-sentinel-across-workspaces-tenants
Question 12 Topic 6, Mixed Questions
HOTSPOT
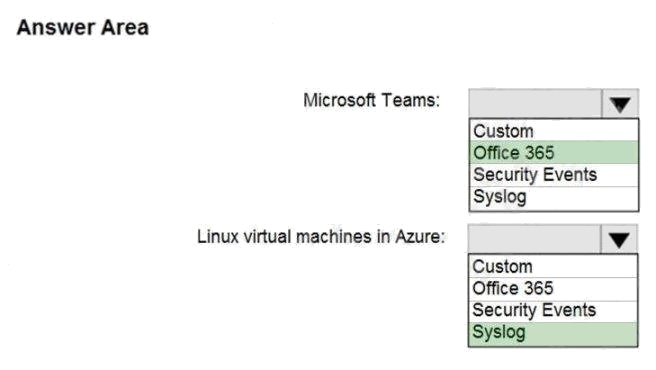
You use Azure Sentinel to monitor irregular Azure activity.
You create custom analytics rules to detect threats as shown in the following exhibit.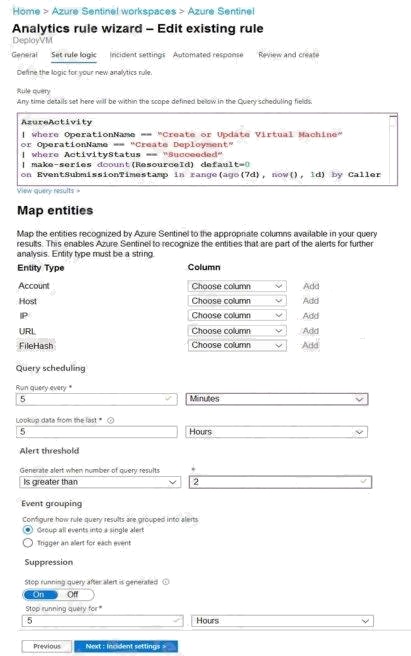
You do NOT define any incident settings as part of the rule definition.
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in
the graphic.
NOTE: Each correct selection is worth one point.
Hot Area:
Answer:
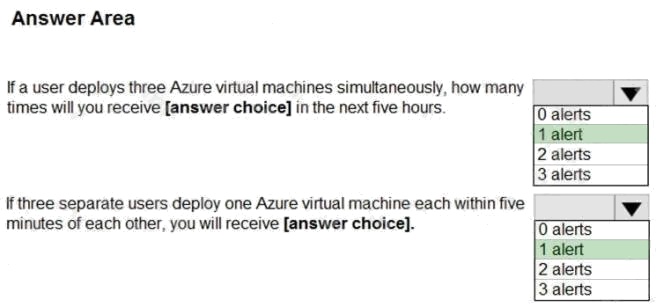
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/tutorial-detect-threats-custom
Question 13 Topic 6, Mixed Questions
A company uses Azure Sentinel.
You need to create an automated threat response.
What should you use?
- A. a data connector
- B. a playbook
- C. a workbook
- D. a Microsoft incident creation rule
Answer:
B
Explanation:
Reference: https://docs.microsoft.com/en-us/azure/sentinel/tutorial-respond-threats-playbook
Question 14 Topic 6, Mixed Questions
DRAG DROP
Your company deploys Azure Sentinel.
You plan to delegate the administration of Azure Sentinel to various groups.
You need to delegate the following tasks:
Create and run playbooks
Create workbooks and analytic rules.
The solution must use the principle of least privilege.
Which role should you assign for each task? To answer, drag the appropriate roles to the correct tasks. Each role may be
used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place: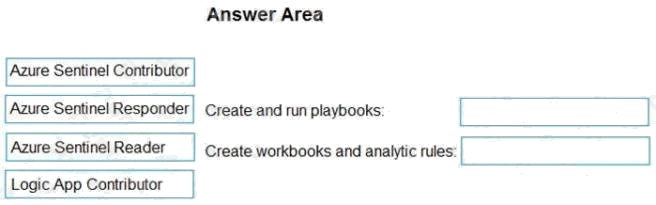
Answer:

Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/roles
Question 15 Topic 6, Mixed Questions
You recently deployed Azure Sentinel.
You discover that the default Fusion rule does not generate any alerts. You verify that the rule is enabled.
You need to ensure that the Fusion rule can generate alerts.
What should you do?
- A. Disable, and then enable the rule.
- B. Add data connectors
- C. Create a new machine learning analytics rule.
- D. Add a hunting bookmark.
Answer:
B
Explanation:
Reference:
https://docs.microsoft.com/en-us/azure/sentinel/connect-data-sources