Question 1
Which statement is correct about IP-IP tunnels?
- A. IP-IP tunnels only support encapsulating IP traffic.
- B. IP-IP tunnels only support encapsulating non-IP traffic.
- C. The TTL in the inner packet is decremented during transit to the tunnel endpoint.
- D. There are 24 bytes of overhead with IP-IP encapsulation.
Answer:
A
Explanation:
IP-IP tunnels are a type of tunnels that use IP as both the encapsulating and encapsulated protocol.
IP-IP tunnels are simple and easy to configure, but they do not provide any security or authentication
features. IP-IP tunnels only support encapsulating IP traffic, which means that the payload of the
inner packet must be an IP packet.
IP-IP tunnels cannot encapsulate non-IP traffic, such as Ethernet
frames or MPLS labels1
.
Option A is correct, because IP-IP tunnels only support encapsulating IP traffic. Option B is incorrect,
because IP-IP tunnels only support encapsulating non-IP traffic. Option C is incorrect, because the
TTL in the inner packet is not decremented during transit to the tunnel endpoint.
The TTL in the outer
packet is decremented by each router along the path, but the TTL in the inner packet is preserved
until it reaches the tunnel endpoint2
. Option D is incorrect, because there are 20 bytes of overhead
with IP-IP encapsulation.
The overhead consists of the header of the outer packet, which has a fixed
size of 20 bytes for IPv43
.
Reference:
:
IP-IP Tunneling 2
:
What is tunneling? | Tunneling in networking 3
: IPv4 - Header
Comments
Question 2
You are configuring an IS-IS IGP network and do not see the IS-IS adjacencies established. In this
scenario, what are two reasons for this problem? (Choose two.)
- A. MTU is not at least 1492 bytes.
- B. IP subnets are not a /30 address.
- C. The Level 2 routers have mismatched areas.
- D. The lo0 interface is not included as an IS-IS interface.
Answer:
AD
Explanation:
Option A suggests that the MTU is not at least 1492 bytes.
This is correct because IS-IS requires a
minimum MTU of 1492 bytes to establish adjacencies1
.
If the MTU is less than this, IS-IS adjacencies
will not be established1
.
Option D suggests that the lo0 interface is not included as an IS-IS interface.
This is also correct
because the loopback interface (lo0) is typically used as the router ID in IS-IS1
.
If the loopback
interface is not included in IS-IS, it could prevent IS-IS adjacencies from being established1
.
Therefore, options A and D are correct.
Comments
Question 3
You are asked to create a new firewall filter to evaluate Layer 3 traffic that is being sent between
VLANs. In this scenario, which two statements are correct? (Choose two.)
- A. You should create a family Ethernet-switching firewall filter with the appropriate match criteria and actions.
- B. You should apply the firewall filter to the appropriate VLAN.
- C. You should create a family inet firewall filter with the appropriate match criteria and actions.
- D. You should apply the firewall filter to the appropriate IRB interface.
Answer:
CD
Explanation:
A firewall filter is a configuration that defines the rules that determine whether to forward or discard
packets at specific processing points in the packet flow. A firewall filter can also modify the attributes
of the packets, such as priority, marking, or logging.
A firewall filter can be applied to various
interfaces, protocols, or routing instances on a Juniper device1
.
A firewall filter has a family attribute, which specifies the type of traffic that the filter can
evaluate.
The family attribute can be one of the following: inet, inet6, mpls, vpls, iso, or ethernet-
switching2
. The family inet firewall filter is used to evaluate IPv4 traffic, which is the most common
type of Layer 3 traffic on a network.
To create a family inet firewall filter, you need to specify the appropriate match criteria and actions
for each term in the filter. The match criteria can include various fields in the IPv4 header, such as
source address, destination address, protocol, port number, or DSCP value.
The actions can include
accept, discard, reject, count, log, policer, or next term3
.
To apply a firewall filter to Layer 3 traffic that is being sent between VLANs, you need to apply the
filter to the appropriate IRB interface. An IRB interface is an integrated routing and bridging interface
that provides Layer 3 functionality for a VLAN on a Juniper device. An IRB interface has an IP address
that acts as the default gateway for the hosts in the VLAN.
An IRB interface can also participate in
routing protocols and forward packets to other VLANs or networks4
.
Therefore, option C is correct, because you should create a family inet firewall filter with the
appropriate match criteria and actions. Option D is correct, because you should apply the firewall
filter to the appropriate IRB interface.
Option A is incorrect, because you should not create a family ethernet-switching firewall filter with
the appropriate match criteria and actions. A family ethernet-switching firewall filter is used to
evaluate Layer 2 traffic on a Juniper device.
A family ethernet-switching firewall filter can only match
on MAC addresses or VLAN IDs, not on IP addresses or protocols5
.
Option B is incorrect, because you should not apply the firewall filter to the appropriate VLAN. A
VLAN is a logical grouping of hosts that share the same broadcast domain on a Layer 2 network. A
VLAN does not have an IP address or routing capability.
A firewall filter cannot be applied directly to
a VLAN; it must be applied to an interface that belongs to or connects to the VLAN6
.
Reference:
:
Firewall Filters Overview 2
:
Configuring Firewall Filters 3
:
Configuring Firewall Filter Match
Conditions and Actions 4
:
Understanding Integrated Routing and Bridging Interfaces 5: Configuring
Ethernet-Switching Firewall Filters 6
: Understanding VLANs
Comments
Question 4
Exhibit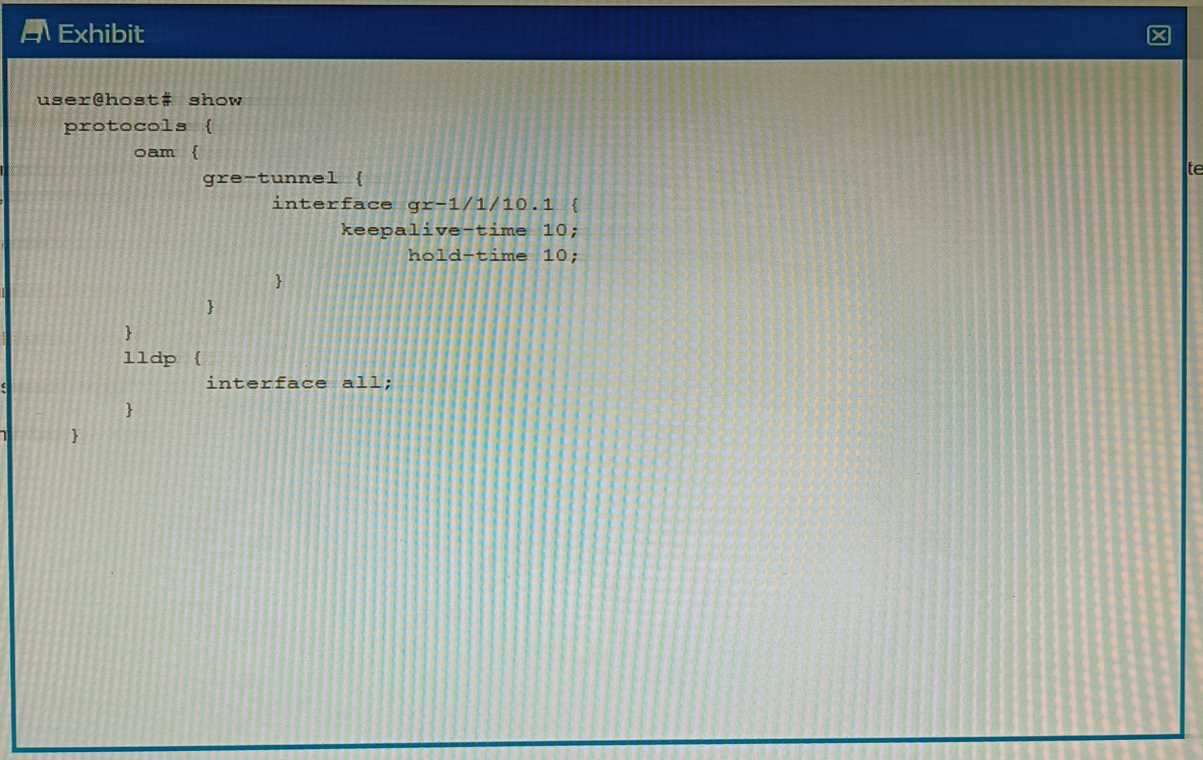
You have configured a GRE tunnel. To reduce the risk of dropping traffic, you have configured a
keepalive OAM probe to monitor the state of the tunnel; however, traffic drops are still occurring.
Referring to the exhibit, what is the problem?
- A. For GRE tunnels, the OAM protocol requires that the BFD protocols also be used.
- B. The "event link-adjacency-loss" option must be set.
- C. LLDP needs to be removed from the gr-1/1/10.1 interface.
- D. The hold-time value must be two times the keepalive-time value
Answer:
D
Explanation:
A keepalive OAM probe is a mechanism that can be used to monitor the state of a GRE tunnel and
detect any failures in the tunnel path. A keepalive OAM probe consists of sending periodic packets
from one end of the tunnel to the other and expecting a reply.
If no reply is received within a
specified time, the tunnel is considered down and the line protocol of the tunnel interface is changed
to down1
.
To configure a keepalive OAM probe for a GRE tunnel, you need to specify two parameters: the
keepalive-time and the hold-time. The keepalive-time is the interval between each keepalive packet
sent by the local router.
The hold-time is the maximum time that the local router waits for a reply
from the remote router before declaring the tunnel down2
.
According to the Juniper Networks documentation, the hold-time value must be two times the
keepalive-time value for a GRE tunnel2
. This is because the hold-time value must account for both
the round-trip time of the keepalive packet and the processing time of the remote router. If the hold-
time value is too small, it may cause false positives and unnecessary tunnel flaps.
In the exhibit, the configuration shows that the keepalive-time is set to 10 seconds and the hold-time
is set to 15 seconds for the gr-1/1/10.1 interface. This means that the local router will send a
keepalive packet every 10 seconds and will wait for 15 seconds for a reply from the remote router.
However, this hold-time value is not two times the keepalive-time value, which violates the
recommended configuration. This may cause traffic drops if the remote router takes longer than 15
seconds to reply.
Therefore, option D is correct, because the hold-time value must be two times the keepalive-time
value for a GRE tunnel.
Option A is incorrect, because BFD is not required for GRE tunnels; BFD is
another protocol that can be used to monitor tunnels, but it is not compatible with GRE
keepalives3
.
Option B is incorrect, because the “event link-adjacency-loss” option is not related to
GRE tunnels; it is an option that can be used to trigger an action when a link goes down4
.
Option C is
incorrect, because LLDP does not need to be removed from the gr-1/1/10.1 interface; LLDP is a
protocol that can be used to discover neighboring devices and their capabilities, but it does not
interfere with GRE tunnels5
.
Reference:
:
Configuring Keepalive Time and Hold time for a GRE Tunnel Interface 2: keepalive | Junos OS |
Juniper Networks 3: Configuring Bidirectional Forwarding Detection 4: event link-adjacency-loss |
Junos OS | Juniper Networks 5
: Understanding Link Layer Discovery Protocol
Comments
Question 5
Exhibit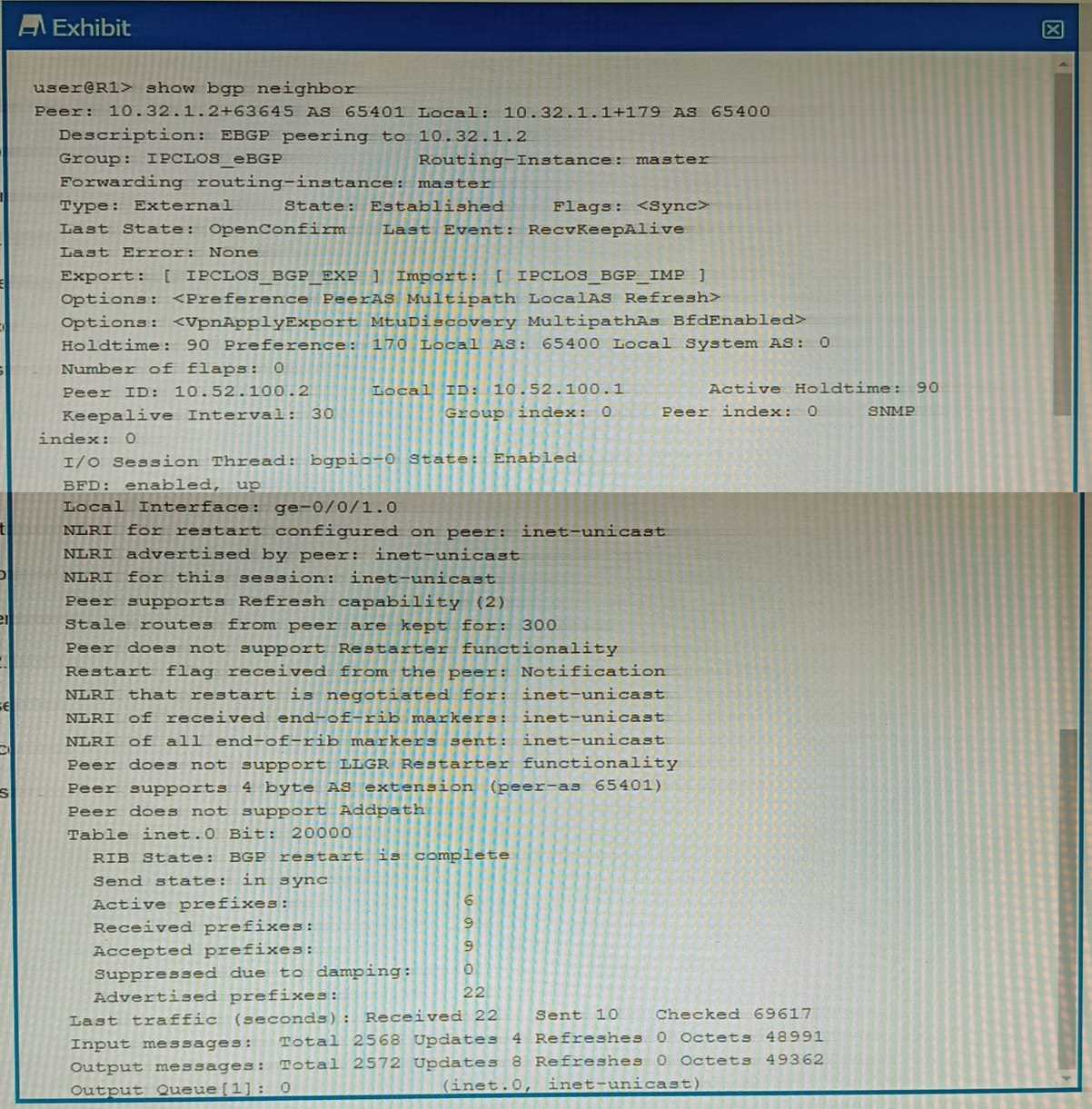
You are a network operator troubleshooting BGP connectivity.
Which two statements are correct about the output shown in the exhibit? (Choose two.)
- A. Peer 10.32.1.2 is configured for AS 63645.
- B. The BGP session is not established.
- C. The R1 is configured for AS 65400.
- D. The routers are exchanging IPv4 routes.
Answer:
BC
Explanation:
Option B suggests that the BGP session is not established. This is correct because in the output, the
state of the BGP session is shown as “Idle”.
In BGP, an “Idle” state means that the BGP session is not
currently established1
.
Option C suggests that R1 is configured for AS 65400.
This is also correct because in the output, it’s
shown that the local AS number is 654001
.
The local AS number represents the Autonomous System
(AS) number of the router on which you’re checking the BGP session1
.
Comments
Question 6
What is the maximum allowable MTU size for a default GRE tunnel without IPv4 traffic
fragmentation?
- A. 1496 bytes
- B. 1480 bytes
- C. 1500 bytes
- D. 1476 bytes
Answer:
D
Explanation:
The maximum allowable MTU size for a default GRE tunnel without IPv4 traffic fragmentation is 1476
bytes1
.
This is because GRE packets are formed by the addition of the original packets and the
required GRE headers1
.
These headers are 24-bytes in length and since these headers are added to
the original frame, depending on the original size of the packet we may run into IP MTU
problems1
.
The most common IP MTU is 1500-bytes in length (Ethernet)1
.
When the tunnel is
created, it deducts the 24-bytes it needs to encapsulate the passenger protocols and that is the IP
MTU it will use1
.
For example, if we are forming a tunnel over FastEthernet (IP MTU 1500) the IOS
calculates the IP MTU on the tunnel as: 1500-bytes from Ethernet - 24-bytes for the GRE
encapsulation = 1476-Bytes1
.
Comments
Question 7
You are a network operator who wants to add a second ISP connection and remove the default route
to the existing ISP You decide to deploy the BGP protocol in the network.
What two statements are correct in this scenario? (Choose two.)
- A. IBGP updates the next-hop attribute to ensure reachability within an AS.
- B. IBGP peers advertise routes received from EBGP peers to other IBGP peers.
- C. IBGP peers advertise routes received from IBGP peers to other IBGP peers.
- D. EBGP peers advertise routes received from IBGP peers to other EBGP peers.
Answer:
AB
Explanation:
A is correct because IBGP updates the next-hop attribute to ensure reachability within an AS. This is
because the next-hop attribute is the IP address of the router that advertises the route to a BGP peer.
If the next-hop attribute is not changed by IBGP, it would be the IP address of an external router,
which may not be reachable by all routers within the AS.
Therefore, IBGP updates the next-hop
attribute to the IP address of the router that received the route from an EBGP peer1
.
B is correct because IBGP peers advertise routes received from EBGP peers to other IBGP peers. This
is because BGP follows the rule of advertising only the best route to a destination, and EBGP routes
have a higher preference than IBGP routes.
Therefore, IBGP peers advertise routes learned from an
EBGP peer to all BGP peers, including both EBGP and IBGP peers1
.
Comments
Question 8
You are troubleshooting a BGP routing issue between your network and a customer router and are
reviewing the BGP routing policies. Which two statements are correct in this scenario? (Choose two.)
- A. Export policies are applied to routes in the RIB-ln table.
- B. Import policies are applied to routes in the RIB-Local table.
- C. Import policies are applied after the RIB-ln table.
- D. Export policies are applied after the RIB-Local table.
Answer:
CD
Explanation:
In BGP, routing policies are used to control the flow of routing information between BGP peers1
.
Option C suggests that import policies are applied after the RIB-In table.
This is correct because
import policies in BGP are applied to routes that are received from a BGP peer, before they are
installed in the local BGP Routing Information Base (RIB-In)1
.
The RIB-In is a database that stores all
the routes that are received from all peers1
.
Option D suggests that export policies are applied after the RIB-Local table.
This is correct because
export policies in BGP are applied to routes that are being advertised to a BGP peer, after they have
been selected from the local BGP Routing Information Base (RIB-Local)1
.
The RIB-Local is a database
that stores all the routes that the local router is using1
.
Therefore, options C and D are correct.
Comments
Question 9
You are asked to connect an IP phone and a user computer using the same interface on an EX Series
switch. The traffic from the computer does not use a VLAN tag, whereas the traffic from the IP phone
uses a VLAN tag.
Which feature enables the interface to receive both types of traffic?
- A. native VLAN
- B. DHCP snooping
- C. MAC limiting
- D. voice VLAN
Answer:
D
Explanation:
The feature that enables an interface on an EX Series switch to receive both untagged traffic (from
the computer) and tagged traffic (from the IP phone) is the voice VLAN12
.
The voice VLAN feature in EX-series switches enables access ports to accept both data (untagged)
and voice (tagged) traffic and separate that traffic into different VLANs12
.
This allows the switch to
differentiate between voice and data traffic, ensuring that voice traffic can be treated with a higher
priority12
. Therefore, option D is correct.
Comments
Question 10
Exhibit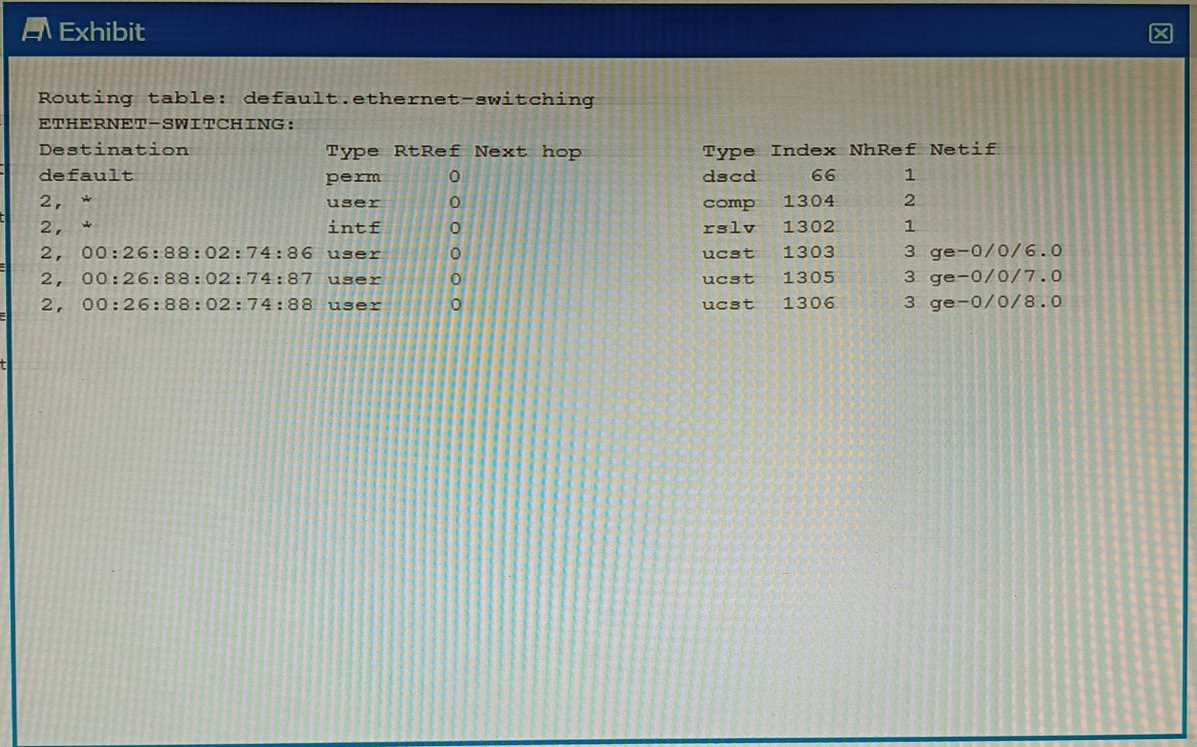
Which command displays the output shown in the exhibit?
- A. show route forwarding-table
- B. show ethernet-switching table
- C. show ethernet—switching table extensive
- D. show route forwarding—table family ethernet-switching
Answer:
B
Explanation:
The output shown in the exhibit is a brief display of the Ethernet switching table, which shows the
learned Layer 2 MAC addresses for each VLAN and interface1
.
The command show ethernet-switching table displays the Ethernet switching table with brief
information, such as the destination MAC address, the VLAN name, the forwarding state, and the
interface name1
.
The command show route forwarding-table displays the routing table information for each protocol
family, such as inet, inet6, mpls, iso, and so on2
. It does not show the Ethernet switching table or the
MAC addresses.
The command show ethernet-switching table extensive displays the Ethernet switching table with
extensive information, such as the destination MAC address, the VLAN name, the forwarding state,
the interface name, the VLAN index, and the tag type1
. It shows more details than the brief output
shown in the exhibit.
The command show route forwarding-table family ethernet-switching displays the routing table
information for the ethernet-switching protocol family, which shows the destination MAC address,
the next-hop MAC address, and the interface name3
. It does not show the VLAN name or the
forwarding state.
Comments
Page 1 out of 6
Viewing questions 1-10 out of 65
page 2