HP hpe6-a79 practice test
Aruba Certified Mobility Expert Written Exam
Last exam update: Jul 20 ,2024
Question 1
Refer to the exhibits.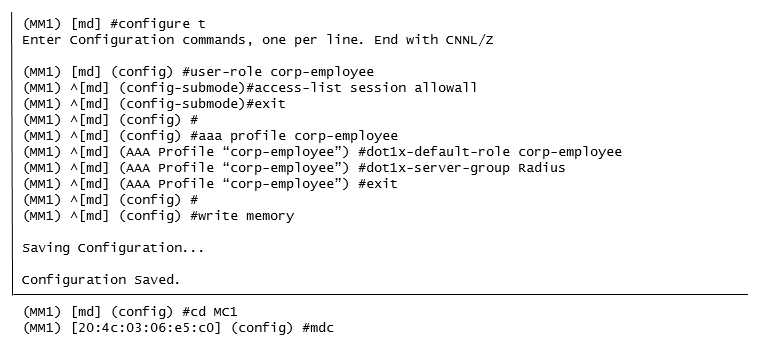
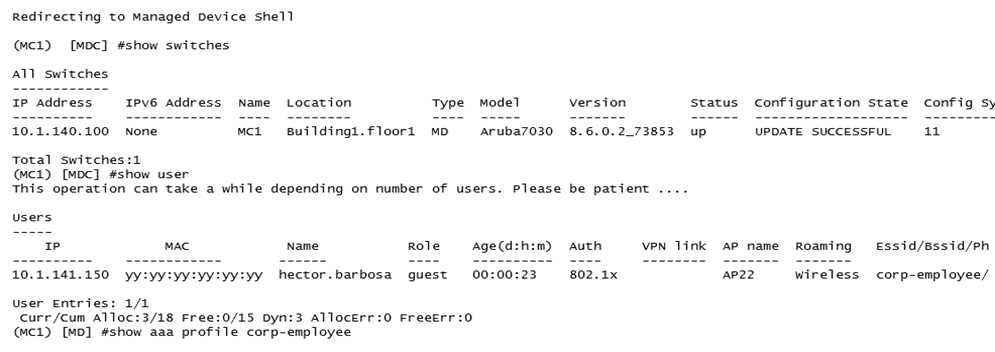
A network administrator has fully deployed a WPA3 based WLAN with 802.1X authentication. Later
he defined corp-employee as the default user-role for the 802.1X authentication method in the aaa
profile. When testing the setup he realizes the client gets the guest role.
What is the reason corp-employee user role was not assigned?
- A. The administrator forgot to map a dotlx profile to the corp-employee aaa profile.
- B. The administrator forgot to enable PEFNG feature set on the Mobility Master.
- C. MC 1 has not received the configuration from the mobility master yet.
- D. The Mobility Master lacks MM-VA licenses; therefore, it shares partial configuration only.
Answer:
C
Question 2
A company with 535 users deploys an Aruba solution with more than 1000 Aruba APs, two 7220
Mobility Controllers, and a single Mobility Master (MM) virtual appliance at the campus server farm.
The MCs run a HA Fast failover group in dual mode and operate at 50% AP capacity.
If there is an MM or MC failure, the network administrator must ensure that the network is fully
manageable and the MC load does not exceed 80%.
What can the network administrator do to meet these requirements?
- A. Place the APs in the same hierarchy level.
- B. Create a cluster with AP load balancing.
- C. Enable oversubscription in the HA group.
- D. Add an MC and an MM in the server farm.
- E. Add an MM and enable DC redundancy.
- F. Place the APs in two different AP-Groups.
Answer:
E
Question 3
Users run Skype for Business on wireless clients with no WMM support over an Aruba Mobility
Master (MM) - Mobility Controller (MC) based network. When traffic arrives at the wired network, it
does not include either L2 or L3 markings.
Which configuration steps should the network administrator take to classify and mark voice and
video traffic with UCC heuristics mode?
- A. Enable WMM in a VAP profile, and explicitly permit voice and video UDP ports in a firewall policy.
- B. Confirm OpenFlow is enabled in the user role and VAP profile. Then enable WMM in a SSID profile, and explicitly permit voice and video UDP ports in a firewall policy.
- C. Confirm the MC is the Openflow controller of the MMs and Openflow is enabled in VAP and firewall roles. Enable Skype4Business ALG in UCC profiles.
- D. Confirm MM is the Openflow controller of MCs and Openflow is enabled in VAP and firewall roles. Enable Skype4Business ALG in UCC profiles.
Answer:
A
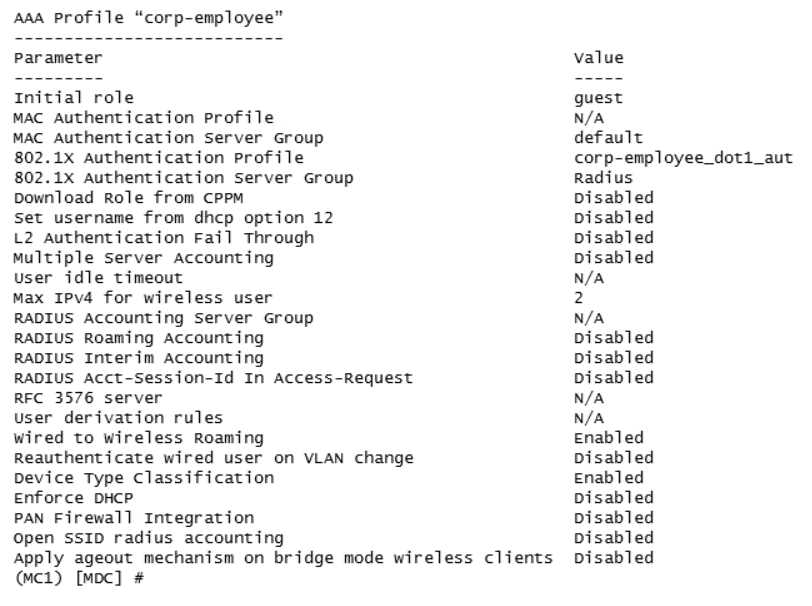
Question 4
A network administrator wants to permit explicit SSH, FTP and HHTP(s) access to servers in the
10.100.20.5 to 10.100.20.31 range, all devices in 10.100.21.0/24 network, and a host with IP address
10.100.22.70. The services must work properly at all times.
Which configuration scripts accomplish this task with the fewer number of lines, while avoiding
access to other devices not included in these ranges? (Choose two.)
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer:
AB
Question 5
Refer to the exhibits.
Exhibit 1
Exhibit 2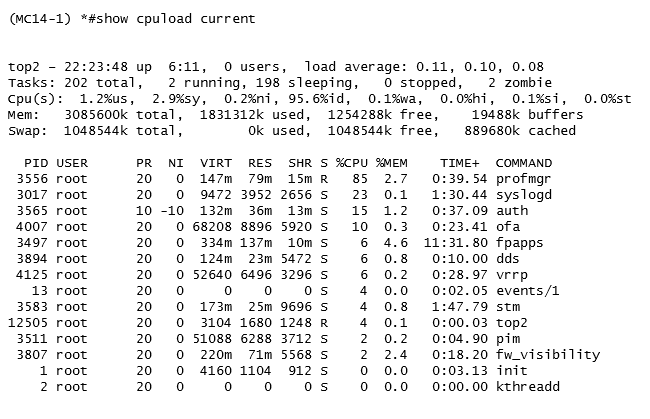
A network administrator adds a new Mobility Controller (MC) to the production Mobility Master
(MM) and deploys APs that start broadcasting the employee SSID in the West wing of the building.
Suddenly, the employees report client disconnects. When accessing the MM the network
administrator notices that the MC is unreachable, then proceeds to access the MCs console and
obtains the outputs shown in the exhibits.
What should the network administrator do next to solve the current problem?
- A. Open a TAC case and send the output of tar crash.
- B. Kill two zombie processes then reboot the MC.
- C. Verify the license pools in the MM.
- D. Decommission the MC from the MM, and add it again.
Answer:
C
Question 6
Refer to the exhibit.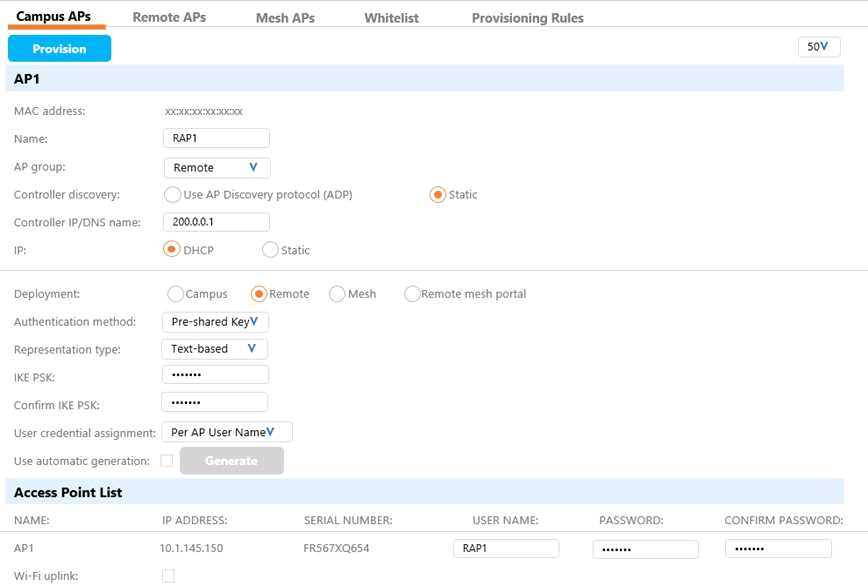
A network administrator has a Mobility Master (MM) Mobility Controller (MC) architecture along
with the MC in the DMZ for terminating RAPs. The network firewall has been provisioned to allow
access to the MC in the DMZ for both UDP 500 and 4500. Then he proceeds to provision an AP as
shown in the exhibit.
Which additional configuration steps must the administrator to assure RAPs successfully contact the
MC? (Choose two.)
- A. Create the RAP1 account in the InternalDB of the MC.
- B. Create an IP local pool and PSK at the device node level.
- C. Create the RAP1 account in the InternalDB of the MM.
- D. Add the RAP1 entry in the CPsec whitelist at the MM level.
- E. Create an IP local pool and PSK at the /mm/mynode level.
Answer:
DE
Question 7
Refer to the exhibit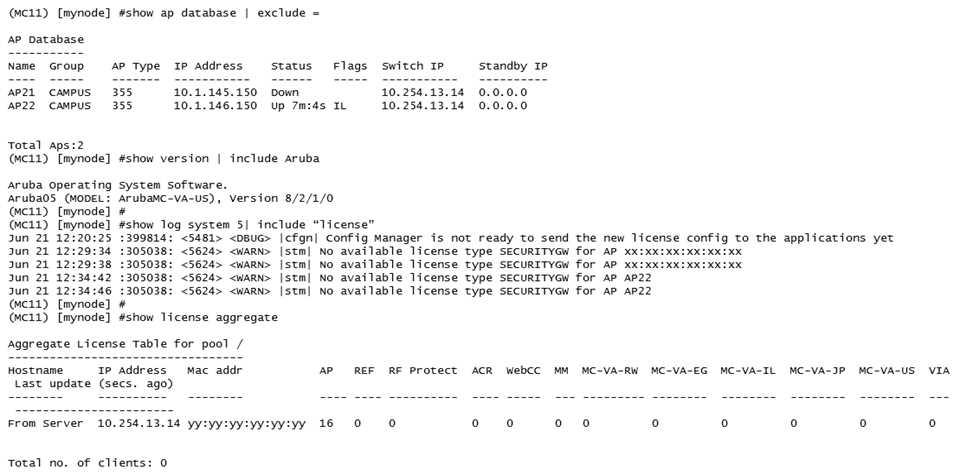
A network administrator deploys a standalone Mobility Controller (MC) and configures some VAPs
within the CAMPUS AP group. The network administrator realizes that none of the VAPs are being
broadcasted.
Based on the output shown in the exhibit, what should the network administrator do to solve this
problem?
- A. Install MC-VA licenses, then install PEF licenses and enabled the PEF feature.
- B. Install MC-VA licenses, then reprovision the APs.
- C. Install MM licenses, then install PEF licenses and enable the PEF feature.
- D. Install MM licenses and install MC-VA licenses, then install RFP licenses.
Answer:
D
Question 8
Refer to the exhibit.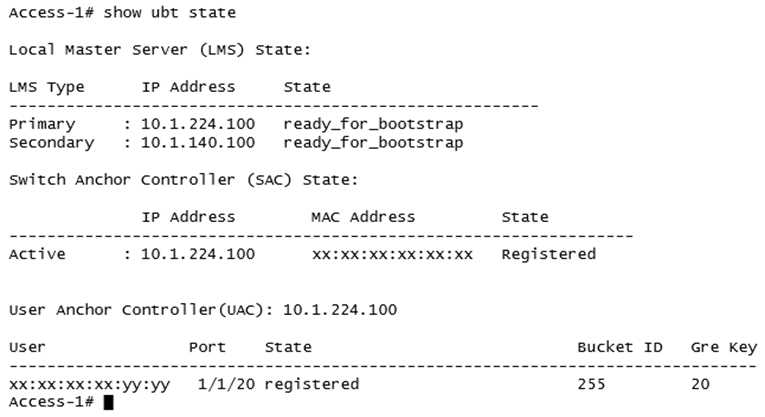
Based on the output shown in the exhibit, with which Aruba devices has Access-1 established
tunnels?
- A. a pair of standalone MCs
- B. a pair of switches running VXLAN
- C. a pair of MCs within a L3 cluster
- D. a single standalone MC
Answer:
C
Question 9
Refer to the exhibit.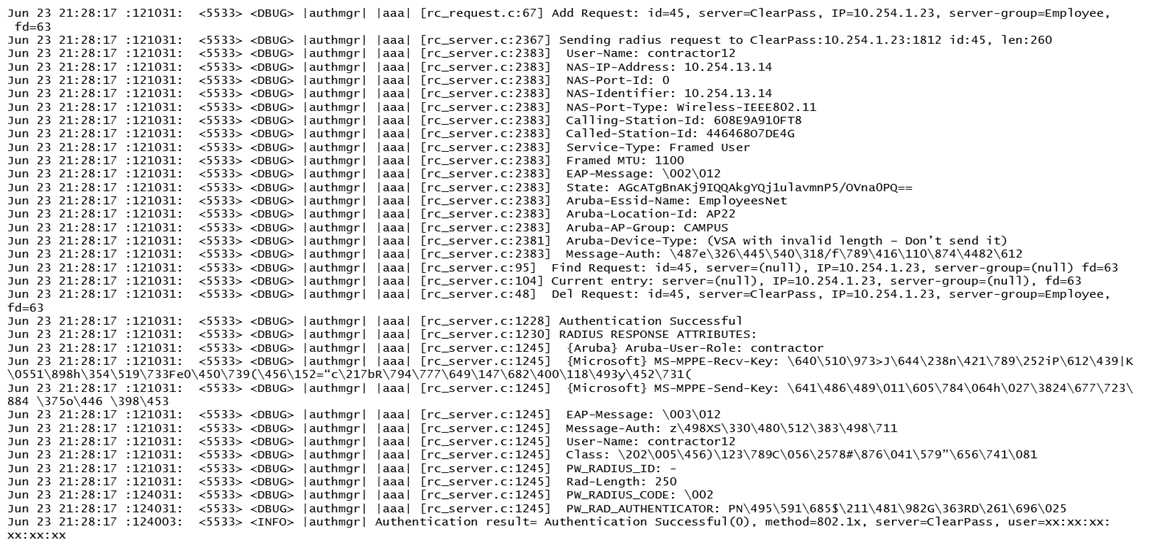
A network administrator wants to allow contractors to access the WLAN named EmployeesNet. In
order to restrict network access, the network administrator wants to assign this category of users to
the contractor user role. To do this, the network administrator configures ClearPass in a way that it
returns the Aruba-User-Role with the contractor value.
When testing the solution, the network administrator receives the wrong role.
What should the network administrator do to assign the contractor role to contractor users without
affecting any other role assignment?
- A. Check the Download role from the CPPM option in the AAA profile.
- B. Set contractor as the default role in the AAA profile.
- C. Create Contractor firewall role in the M.
- D. Create server deviation rules in the server group.
Answer:
A
Reference:
https://www.arubanetworks.com/techdocs/ClearPass/6.7/Aruba_DeployGd_HTML/Content/Aruba%
20Controller%20Configuration/AAA_profile_adding.htm
Question 10
A network administrator has deployed an Airwave Management Platform (AMP) server and
integrated it with a Mobility Master (MM) Mobility Controller (MC) based WLAN. The AMP server
already has all Aruba Mobility devices including Access Points (APs) in the UP devices list.
What are two actions the administrator can execute upon the APs under
Airwave>Devices>Monitor? (Choose two.)
- A. Open the WebUI of the MC where the AP terminates.
- B. Re-provision the Access Point.
- C. Disable and change the mode of the AP's radios.
- D. Invoke MC's show commands for that Access Point.
- E. Run Spectrum Analysis locally.
Answer:
DE
Question 11
A network administrator assists with the migration of a WLAN from a third-party vendor to Aruba in
different locations throughout the country. In order to manage the solution from a central point, the
network administrator decides to deploy redundant Mobility Masters (MMs) in a datacenter that are
reachable through the Internet.
Since not all locations own public IP addresses, the security team is not able to configure strict
firewall polices at the datacenter without disrupting some MM to Mobility Controller (MC)
communications. They are also concerned about exposing the MMs to unauthorized inbound
connection attempts.
What should the network administrator do to ensure the solution is functional and secure?
- A. Deploy an MC at the datacenter as a VPN concentrator.
- B. Block all inbound connections, and instruct the MM to initiate the connection to the MCs.
- C. Block all ports to the MMs except UDP 500 and 4500.
- D. Install a PEFV license, and configure firewall policies that protect the MM.
Answer:
C
Question 12
A software development company has 764 employees who work from home. The company also has
small offices located in different cities throughout the world. During working hours, they use RAPs to
connect to a datacenter to upload software code as well as interact with databases.
In the past two month, cabling issues have occurred connection to the 7240XM Mobility Controller
(MC) that runs ArubaOS 8 and terminates the RAPs. These RAPs disconnect, affecting the users
connected to the RAPs. This also causes problems with code uploads and database synchronizations.
Therefore, the company decides to add a second 7240XM controller for redundancy.
How should the network administrator deploy both controllers in order to provide the redundancy
while preventing failover events from disconnecting users?
- A. Connect both controllers with common VLANs. and create an HA fast failover group with public addresses in the internet VLAN.
- B. Connect both controllers with common VLANs. and create an L2-connected cluster using public addresses in the internet VLAN.
- C. Connect both controllers with different VLANs. and create an L2-connected cluster using public addresses in the internet VLAN.
- D. Connect both controllers with common VLANs. and configure LMS/BLMS values equal to public addresses in the internet VLAN.
Answer:
A
Question 13
A network administrator has updated the ArubaOS code of a standalone Mobility Controller (MC)
that is used for User-Based Tunneling (UBT) to a newer early release. Ever since the MC seems to
reject PAPI sessions from the switch with the 10.1.10.10 IP address. Also the controllers prompt is
now followed by a star mark: (MC_VA) [mynode] *#
When opening a support ticket, an Aruba TAC engineer asks the administrator to gather the crash
logs and if possible replicate UBT connection attempts from the switch while running packet captures
of PAPI traffic on the controller and obtain the PCAP files. The administrator has a PC with Wireshark
and TFTP server using the 10.0.20.20 IP address.
What commands must the administrator issue to accomplish these requests? (Choose two.)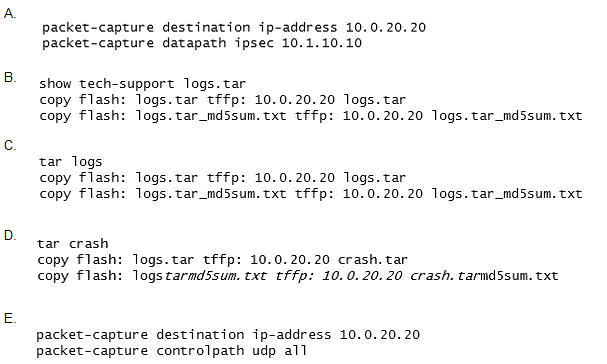
- A. Option A
- B. Option B
- C. Option C
- D. Option D
- E. Option E
Answer:
BE
Question 14
An organization wants to deploy a WLAN infrastructure that provides connectivity to these client
categories:
Employees
Contractors
Guest users
Corporate IoT legacy devices that support no authentication or encryption
Employees and contractors must authenticate with company credentials and get network access
based on AD group membership. Guest users are required to authenticate with captive portal using
predefined credentials. Only employees will run L2 encryption.
Which implementation plan fulfills the requirements while maximizing the channel usage?
- A. Create VAP1 to run WPA2-AES and 802.1x authentication. VAP2 to run opensystem encryption with MAC authentication, and VAP3 to run opensystem with captive portal and L2 fail through.
- B. Create a single VAPto run WPA2-AES and 802.1x authentication. MAC authentication L2 fail through, captive portal, and VIA support.
- C. Create VAP1 to run WPA2-AES and 802.1x authentication. VAP2 to run opensystem encryption with MAC authentication, and VAP3 to run opensystem with captive portal.
- D. Create VAP1 to run WPA2-AES and 802.1x authentication, and VAP2 to run opensystem encryption with MAC authentication and captive portal.
Answer:
D
Question 15
A joint venture between two companies results in a fully functional WLAN Aruba solution. The
network administrator uses the following script to integrate the WLAN solution with two radius
servers, radius1 and radius2.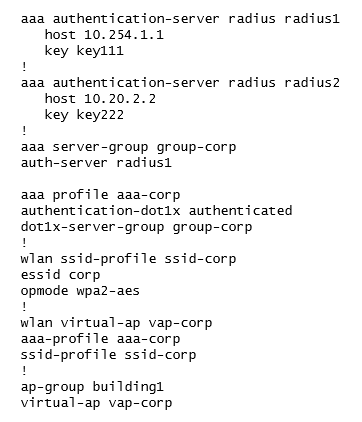
While all users authenticate with [email protected] type of credentials, radius1 has user
accounts with the domain name portion.
Which additional configuration is required to authenticate corp1.com users with radius1 and corp2
users with radius2?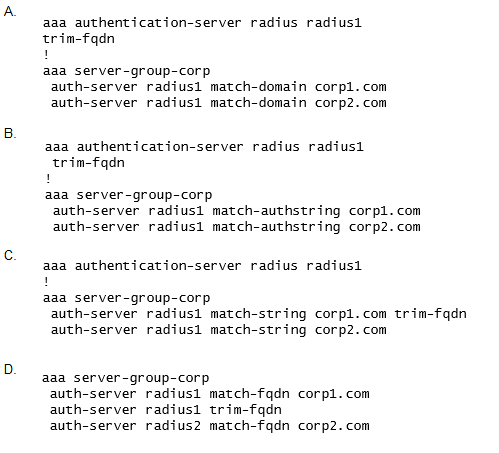
- A. Option A
- B. Option B
- C. Option C
- D. Option D
Answer:
A