google professional cloud security engineer practice test
Professional Cloud Security Engineer
Last exam update: Jun 23 ,2025
Question 1
A company allows every employee to use Google Cloud Platform. Each department has a Google Group, with all department
members as group members. If a department member creates a new project, all members of that department should
automatically have read-only access to all new project resources. Members of any other department should not have access
to the project. You need to configure this behavior.
What should you do to meet these requirements?
- A. Create a Folder per department under the Organization. For each departments Folder, assign the Project Viewer role to the Google Group related to that department.
- B. Create a Folder per department under the Organization. For each departments Folder, assign the Project Browser role to the Google Group related to that department.
- C. Create a Project per department under the Organization. For each departments Project, assign the Project Viewer role to the Google Group related to that department.
- D. Create a Project per department under the Organization. For each departments Project, assign the Project Browser role to the Google Group related to that department.
Answer:
C
Question 2
Your organization has had a few recent DDoS attacks. You need to authenticate responses to domain name lookups. Which
Google Cloud service should you use?
- A. Cloud DNS with DNSSEC
- B. Cloud NAT
- C. HTTP(S) Load Balancing
- D. Google Cloud Armor
Answer:
A
Explanation:
Reference: https://developers.google.com/speed/public-dns/faq
Question 3
Which type of load balancer should you use to maintain client IP by default while using the standard network tier?
- A. SSL Proxy
- B. TCP Proxy
- C. Internal TCP/UDP
- D. TCP/UDP Network
Answer:
C
Explanation:
Reference: https://registry.terraform.io/providers/hashicorp/google/latest/docs/resources/compute_forwarding_rule
Question 4
Applications often require access to secrets - small pieces of sensitive data at build or run time. The administrator
managing these secrets on GCP wants to keep a track of who did what, where, and when? within their GCP projects.
Which two log streams would provide the information that the administrator is looking for? (Choose two.)
- A. Admin Activity logs
- B. System Event logs
- C. Data Access logs
- D. VPC Flow logs
- E. Agent logs
Answer:
A C
Explanation:
Reference: https://cloud.google.com/kms/docs/secret-management
Question 5
You are asked to recommend a solution to store and retrieve sensitive configuration data from an application that runs on
Compute Engine. Which option should you recommend?
- A. Cloud Key Management Service
- B. Compute Engine guest attributes
- C. Compute Engine custom metadata
- D. Secret Manager
Answer:
A
Explanation:
Reference: https://www.freecodecamp.org/news/google-cloud-platform-from-zero-to-hero/
Question 6
You work for a large organization where each business unit has thousands of users. You need to delegate management of
access control permissions to each business unit. You have the following requirements:
Each business unit manages access controls for their own projects.
Each business unit manages access control permissions at scale.
Business units cannot access other business units' projects.
Users lose their access if they move to a different business unit or leave the company.
Users and access control permissions are managed by the on-premises directory service.
What should you do? (Choose two.)
- A. Use VPC Service Controls to create perimeters around each business unit's project.
- B. Organize projects in folders, and assign permissions to Google groups at the folder level.
- C. Group business units based on Organization Units (OUs) and manage permissions based on OUs
- D. Create a project naming convention, and use Google's IAM Conditions to manage access based on the prefix of project names.
- E. Use Google Cloud Directory Sync to synchronize users and group memberships in Cloud Identity.
Answer:
D E
Question 7
You are part of a security team investigating a compromised service account key. You need to audit which new resources
were created by the service account.
What should you do?
- A. Query Data Access logs.
- B. Query Admin Activity logs.
- C. Query Access Transparency logs.
- D. Query Stackdriver Monitoring Workspace.
Answer:
A
Explanation:
Reference: https://cloud.google.com/iam/docs/audit-logging/examples-service-accounts
Question 8
Which two implied firewall rules are defined on a VPC network? (Choose two.)
- A. A rule that allows all outbound connections
- B. A rule that denies all inbound connections
- C. A rule that blocks all inbound port 25 connections
- D. A rule that blocks all outbound connections
- E. A rule that allows all inbound port 80 connections
Answer:
A B
Explanation:
Reference: https://cloud.google.com/vpc/docs/firewalls
Question 9
A company migrated their entire data/center to Google Cloud Platform. It is running thousands of instances across multiple
projects managed by different departments. You want to have a historical record of what was running in Google Cloud
Platform at any point in time.
What should you do?
- A. Use Resource Manager on the organization level.
- B. Use Forseti Security to automate inventory snapshots.
- C. Use Stackdriver to create a dashboard across all projects.
- D. Use Security Command Center to view all assets across the organization.
Answer:
C
Question 10
A customer deployed an application on Compute Engine that takes advantage of the elastic nature of cloud computing.
How can you work with Infrastructure Operations Engineers to best ensure that Windows Compute Engine VMs are up to
date with all the latest OS patches?
- A. Build new base images when patches are available, and use a CI/CD pipeline to rebuild VMs, deploying incrementally.
- B. Federate a Domain Controller into Compute Engine, and roll out weekly patches via Group Policy Object.
- C. Use Deployment Manager to provision updated VMs into new serving Instance Groups (IGs).
- D. Reboot all VMs during the weekly maintenance window and allow the StartUp Script to download the latest patches from the internet.
Answer:
D
Question 11
A customer wants to run a batch processing system on VMs and store the output files in a Cloud Storage bucket. The
networking and security teams have decided that no VMs may reach the public internet.
How should this be accomplished?
- A. Create a firewall rule to block internet traffic from the VM.
- B. Provision a NAT Gateway to access the Cloud Storage API endpoint.
- C. Enable Private Google Access on the VPC.
- D. Mount a Cloud Storage bucket as a local filesystem on every VM.
Answer:
B
Question 12
A companys application is deployed with a user-managed Service Account key. You want to use Google-recommended
practices to rotate the key.
What should you do?
- A. Open Cloud Shell and run gcloud iam service-accounts enable-auto-rotate --iam-account=IAM_ACCOUNT.
- B. Open Cloud Shell and run gcloud iam service-accounts keys rotate --iam-account=IAM_ACCOUNT --key=NEW_KEY.
- C. Create a new key, and use the new key in the application. Delete the old key from the Service Account.
- D. Create a new key, and use the new key in the application. Store the old key on the system as a backup key.
Answer:
C
Explanation:
Reference: https://cloud.google.com/iam/docs/understanding-service-accounts
Question 13
Your team needs to configure their Google Cloud Platform (GCP) environment so they can centralize the control over
networking resources like firewall rules, subnets, and routes. They also have an onpremises environment where resources
need access back to the GCP resources through a private VPN connection. The networking resources will need to be
controlled by the network security team.
Which type of networking design should your team use to meet these requirements?
- A. Shared VPC Network with a host project and service projects
- B. Grant Compute Admin role to the networking team for each engineering project
- C. VPC peering between all engineering projects using a hub and spoke model
- D. Cloud VPN Gateway between all engineering projects using a hub and spoke model
Answer:
A
Explanation:
Reference: https://cloud.google.com/docs/enterprise/best-practices-for-enterprise-organizations#centralize_network_control
Question 14
Your team sets up a Shared VPC Network where project co-vpc-prod is the host project. Your team has configured the
firewall rules, subnets, and VPN gateway on the host project. They need to enable Engineering Group A to attach a
Compute Engine instance to only the 10.1.1.0/24 subnet.
What should your team grant to Engineering Group A to meet this requirement?
- A. Compute Network User Role at the host project level.
- B. Compute Network User Role at the subnet level.
- C. Compute Shared VPC Admin Role at the host project level.
- D. Compute Shared VPC Admin Role at the service project level.
Answer:
C
Explanation:
Reference: https://cloud.google.com/vpc/docs/shared-vpc
Question 15
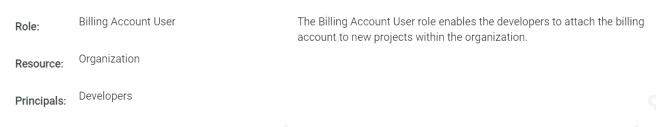
An office manager at your small startup company is responsible for matching payments to invoices and creating billing alerts.
For compliance reasons, the office manager is only permitted to have the
Identity and Access Management (IAM) permissions necessary for these tasks. Which two IAM roles should the office
manager have? (Choose two.)
- A. Organization Administrator
- B. Project Creator
- C. Billing Account Viewer
- D. Billing Account Costs Manager
- E. Billing Account User
Answer:
A E
Explanation:
Reference: https://cloud.google.com/iam/docs/job-functions/billing